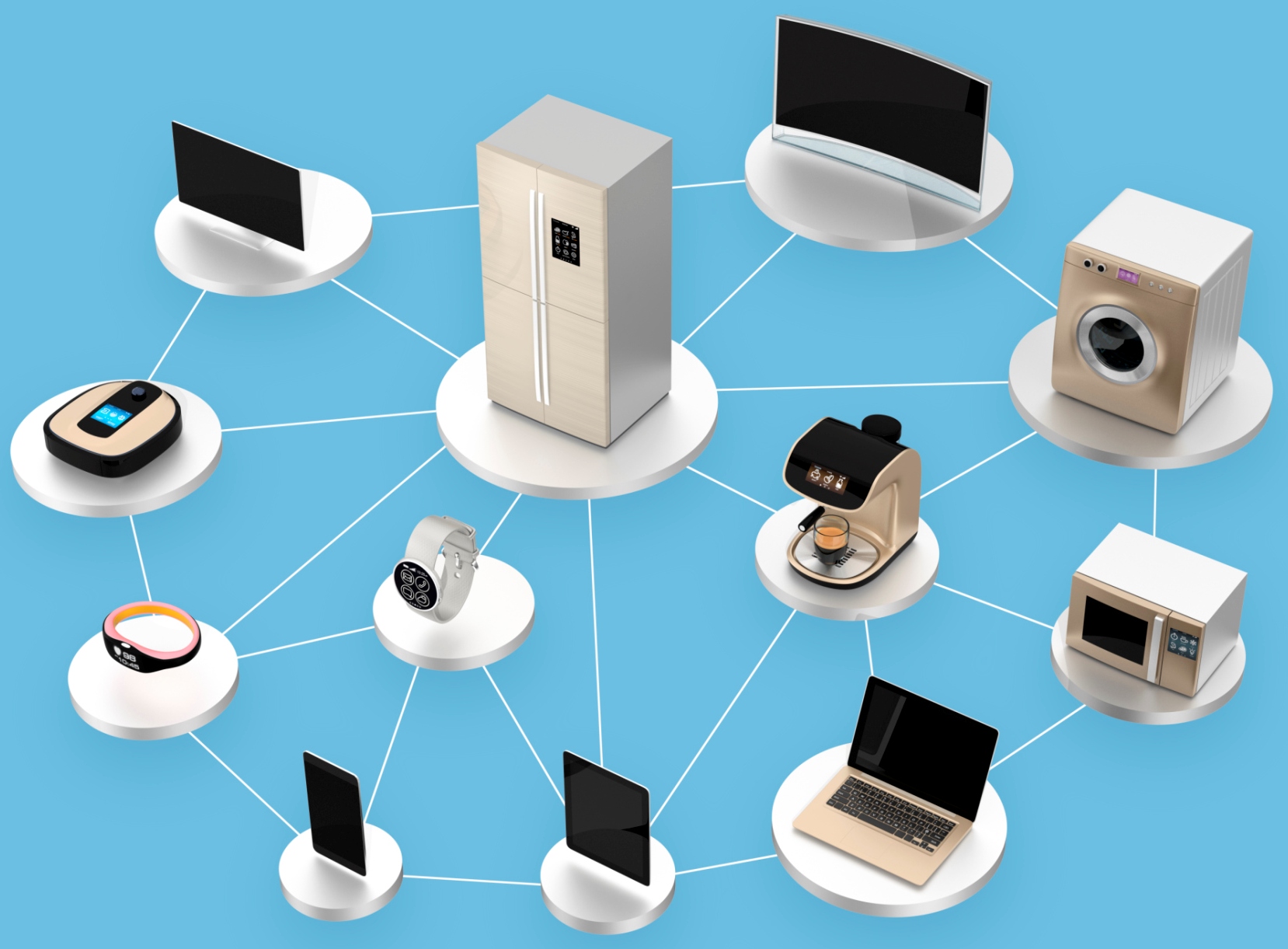
To understand why there is so much excitement surrounding the Internet of Things (IoT), look no further than smart home appliances.
With the ability to remotely control all manner of ‘things’ in our home via smartphone, not only can we turn on the heating as we leave work, but we can heat up our dinner from the car and even unlock the front door as we approach it, says Jonathan Scudder of ForgeRock. Of course, these applications are all quite trivial in the grand scheme of things, but they are a sign of things to come.
There’s growing buzz about the connected car, smart healthcare devices alongside hundreds, if not thousands, of other possibilities that the IoT presents. Analysts at IDC predict IoT spending will exceed $7.3 trillion by 2017. But while all this is great for improving many aspects of our lives, a dark shadow lurks behind it all: concerns about privacy and security.
 With so many different things connecting to the internet, it will come as no surprise that the IoT is leading to a new category of cybercrime. We are already starting to see example of everyday items being used as a route in for hackers. Recently, pen testers revealed that a smart kettle could be leaking Wi-Fi passwords. What does a hack of such a device mean? We haven’t seen one with devastating consequences—yet. But even relatively minor hacks can cause inconvenience for the user. In a lot of these cases the kettles are likely to have been on a home network. However, what if they were connected to a business where there’s a lot more at stake? These vulnerabilities could break the customers’ trust and tarnish a company’s brand reputation, which can irreparably damage its business.
With so many different things connecting to the internet, it will come as no surprise that the IoT is leading to a new category of cybercrime. We are already starting to see example of everyday items being used as a route in for hackers. Recently, pen testers revealed that a smart kettle could be leaking Wi-Fi passwords. What does a hack of such a device mean? We haven’t seen one with devastating consequences—yet. But even relatively minor hacks can cause inconvenience for the user. In a lot of these cases the kettles are likely to have been on a home network. However, what if they were connected to a business where there’s a lot more at stake? These vulnerabilities could break the customers’ trust and tarnish a company’s brand reputation, which can irreparably damage its business.
Identifying who’s who and what’s what has never been so complex. It’s not just about protecting IoT devices but the entire ecosystem, from the customer to the partner, the web page, the mobile device, the mobile app, the cloud and everything else in between. Static and portable devices need to communicate with each other, and human-to-machine and machine-to-machine identification and interaction must be taken into account. Without the right model in place, your organisation could be at risk of making your data—and your customers’—openly available to cyber attacks.
The IoT requires a new way of thinking and acting, one that will protect a business and help it grow. To ensure security in the era of IoT, organisations must consider the following:
1. Security beyond the firewall – IT needs to authenticate customers outside the firewall. Users may want to access systems via multiple devices, and they will expect a user experience that is tailored to how, when, and where they access services.
2. Unify the ecosystem – Trying to duct-tape security architecture together or protect access on a device-by-device basis is not going to work effectively—or even at all. A single platform that unifies the entire ecosystem will provide a simple, repeatable way to protect a growing number of devices.
3. Remain flexible – Building a platform that supports and unifies the entire ecosystem is challenging enough, but you also need to keep the future in mind. Businesses need to support new services, new devices, and new infrastructure on the back end. Open source gives IT a platform it can build on and customise while open standards offer the flexibility to adapt to future needs in a very standardised manner.

4. Understand data usage patterns – How do enterprises protect data they can’t see as it’s communicated between IoT devices and other parts of the ecosystem? Ensuring data is encrypted and authenticated is important. However, it’s also important to understand the relationship between different parts of the ecosystem. Knowing who accesses data and how, where, and when they access it are just a few of the factors that can help ensure proper security. This knowledge helps you verify the user is legitimate and that current behavior is consistent with past behaviour. Because organisations collect all this information, businesses now have a platform they can leverage to better understand and serve the needs of their customers and to provide up-sell opportunities that generate new revenue streams.
Savvy organisations will go to great lengths to protect their customers. We’ve all seen the negative impact mega data-breaches have on organisations. Being smart about security not only helps the CEO keep his or her job, it helps to protect the brand and provides an opportunity to turn the cost of IoT security on its head by using it to provide new and valuable avenues for future growth. Isn’t that what the board really wants in the first place? According to a recent Gartner report, CEOs list “growth” among their top three business priorities and are investing heavily in their digital businesses to achieve this goal. IoT will surely play a significant role in achieving this growth, but if it is implemented without proper security, CEOs will fail before they have a chance to succeed.
The author is Jonathan Scudder, co-founder & chief architect, ForgeRock.
Comment on this article below or via Twitter: @M2MNow OR @jcm2m










