In his regular new column on developments in the Internet of Things (IoT) ecosystem, Antony Savvas explores some evolving industry viewpoints on deployment and security.
There has been, and there will continue to be a whole lot of industry discussion about how to manage the explosion (or should we say tsunami?) of devices that are forming the Internet of Things (IoT). Little wonder, because this particular explosion is barely controlled by the IT industry – so much of it is arriving ‘left field’ from other business sectors.
Previous big, impactful explosions – personal computers, networks, smartphones, the cloud, etc. – have been created and driven by Information Technology. The industry was responsible for persuading people to buy these products and responsible for building and delivering them. But in the case of IoT, and specifically the Industrial Internet of Things (IIoT), the industry is offering as much a service as a product – and there is a whole population of devices out there just waiting to be fitted with chips and connected to the IoT.
Sell a PC or smartphone and you are selling a complete package that complies with a host of regulations and standards, but sell 5G connectivity and you may not be certain if it is for a medical device, for tracking containers, for a utility meter, a drone controller or whatever.
Managing the newcomers
So the IT industry is feeling anxious about opening wide the internet to a vast population of newcomers. Kevin Restivo, IDC’s research manager for European enterprise mobility, led a conference session at the recent NetEvents EMEA IT Spotlight in Barcelona, entitled “They’re Everywhere! Managing the Incredible Explosion of IoT and IIoT Devices”.
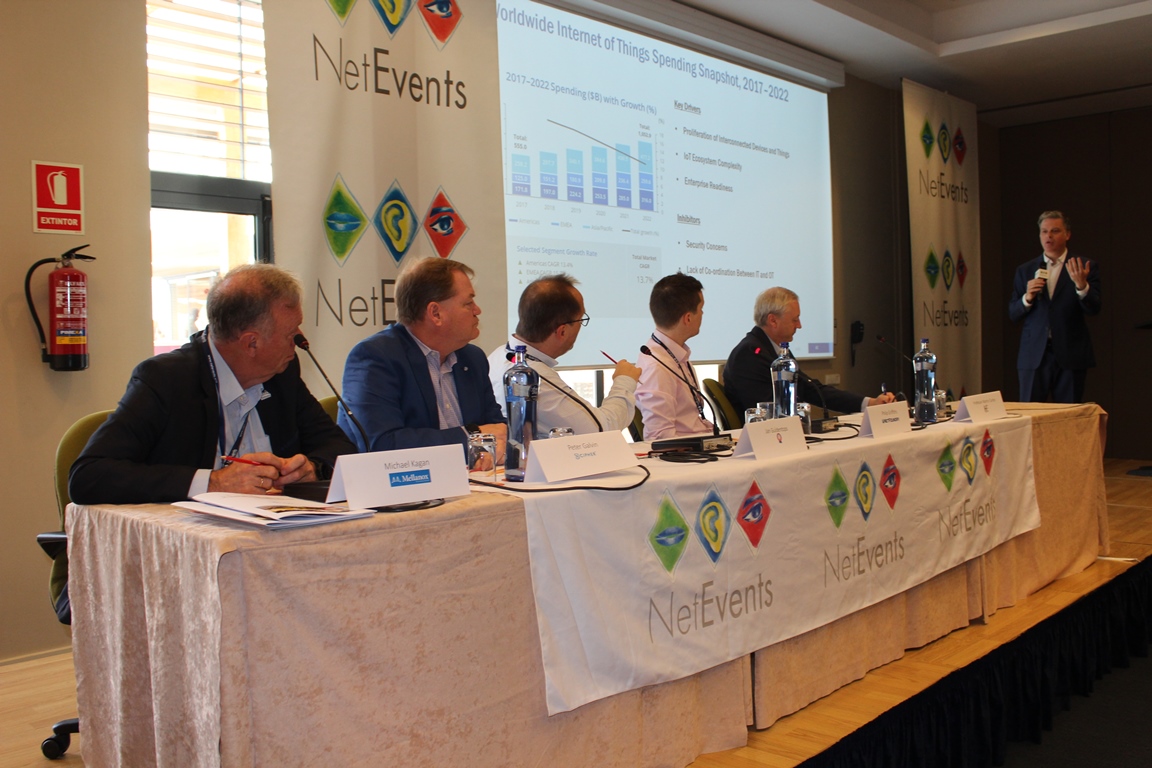
Restivo said: “IoT is one of the fastest growing markets or collection of technologies relative to the ICT (information & communications technology) spectrum. The ecosystem is really a complex mix of technologies and services… server, storage, analytics, IT services, security and a range of other technologies… essentially a wide span of the ICT spectrum.”
This diversity, he said, makes it harder to pin down the elements of spending. Up until now, about a third of it has been on IoT devices and similar amounts on software and services. But in future forecasts he expected much more spending on analytics, as business begins to extract value from its IoT and to optimise its processes.
As to drivers, he added, obviously the explosion of devices is a major factor, as is ecosystem complexity. That last point might sound more like an inhibitor, until you consider the vast array of systems and protocols offered. “That complexity is driving a lot of spending,” said Restivo. A third driver, enterprise readiness, reflects the almost limitless population of devices and systems already out there and waiting to get connected, he said.
As to the inhibitors, security fears lead. Restivo said: “A lack of coordination between operations and IT is very much an inhibitor to deployment. Close collaboration between IT and operational departments is necessary and yet it doesn’t happen.
“Everyone wants to protect their fiefdoms or they’re simply not able or willing to cooperate… IT is often left behind during the project planning, budgeting and piloting. That lack of coordination can really stall the successful deployment of IIoT initiatives.”
Little focus on consumer IoT security
In response to Restivo, Peter Galvin, chief strategy and marketing officer at nCipher Security, compared the fast growing IoT consumer segment, “with very little focus on security”, to the IIoT space – which is “a little more thoughtful” – as well as the already highly regulated medical segment used by both consumers and healthcare professionals.
Jan Guldentops, director for BA Test Labs, pointed out that there was still a massive difference between parking sensors – sending tiny amounts of non-critical data – and industrial systems with hundreds of sensors controlling millions of dollars worth of equipment: “It’s like cloud all over again [in terms of the industry finding its way in addressing a new market].”
Philip Griffiths, head of EMEA partnerships at NetFoundry, commented that while security was still the greatest inhibitor, some organisations are actively seeking solutions: “I’m working on an engagement at the moment where a Fortune 10 company is rolling out an IoT solution.
“They’re not involving IT because they want to move as quickly as possible. But the partner we’re working with, who’s an ISV (independent software vendor), came to us and said, ‘we need to make sure the solution is very secure so that when IT do come along, we can say “this is more secure than your corporate network so there’s nothing for you to worry about”’.”
Health benefits
Moving on to business benefits as drivers for the industry, professor Martin Curley, director of digital transformation and open innovation at the UK’s Health Service Executive, said we should expect a consumerisation of healthcare on a scale to match the consumerisation of IT.

Referring to a book, with the great title, “The Patient Will See You Now”, he suggested: “We will have patients routinely showing up to their cardiologist or to their nephrologist with much better information than the consultants.
“The Apple Watch with its ECG is already an FDA-regulated device. It can detect atrial fibrillation. It could be life-saving.”
He explained that “vital signs” is the term for the key predictors that nurses use to determine if a patient is deteriorating and, in a traditional manual system based on hand-written notes, over 50% of those scores can be wrong. SyncroPhi though has developed a solution to automatically connect, collect and display these vital signs. He saw many diverse opportunities in healthcare: “I think the biggest untapped market is going to be healthcare.”
Michael Kagan, chief technology officer of Mellanox Technologies, rounded up the discussion by proposing the need to identify and understand the interfaces and not mix too many things together: “Segregation of the infrastructure and the computing and application enables you to update these two tiers absolutely independently…don’t tie things too much together, so you can update them and manage and provision them independently.”
The author is freelance technology writer, Antony Savvas.
Comment on this article below or via Twitter: @IoTNow_OR @jcIoTnow










