Enterprises around the globe have been adopting Internet of Things (IoT) products to improve organisational efficiency, enhance communications, and to gain insight into system performance. IoT devices have become commonplace in enterprises from all industries. According to Gartner, 20.4 billion IoT devices will be in use worldwide by 2020, and more than 65% of enterprises will adopt IoT products.
The rapid adoption of these devices has opened up new attack vectors for cybercriminals, says Zscaler’s Deepen Desai. Many are employee-owned, and this is just one of the reasons they pose a security concern for businesses. As is often the case, IoT technology has also moved more quickly than the mechanisms available to safeguard these devices and their users.
Researchers have already demonstrated remote hacks on pacemakers and cars. In October 2016, a large distributed denial-of-service (DDoS) attack, leveraging Mirai Botnet, affected DNS servers on the east coast of the United States, disrupting services worldwide. This attack was traced back to hackers infiltrating networks through IoT devices, including wireless routers and connected cameras.
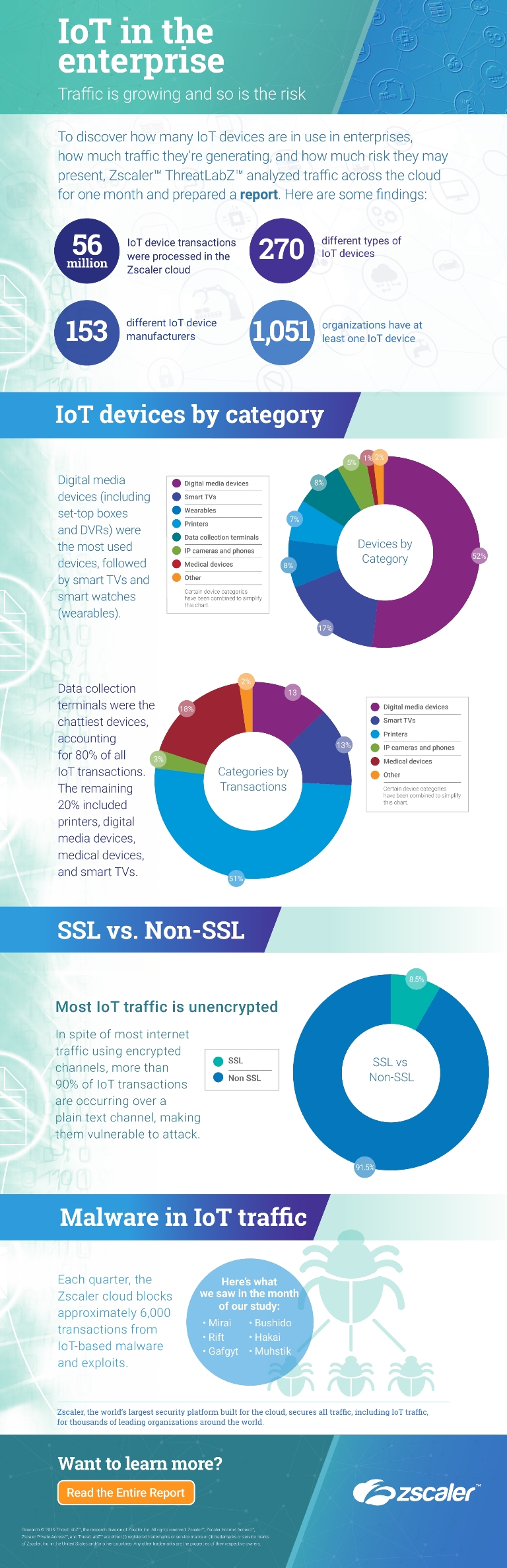
Our own recent research ‘IoT in the Enterprise: an analysis of traffic and threats’, explored some of the security concerns surrounding IoT devices. Among our team’s discoveries was that the vast majority of IoT transactions were occurring over plain text channels, instead of the more secure SSL-encrypted channels. While a major security vulnerability, the use of unsecured channels is just one issue with IoT devices. They are notorious for weak, pre-set passwords that often go unchanged.
As with just about every device connected to the internet, malware is also a threat to IoT devices. The fact is that there has been almost no security built into the IoT hardware devices that have flooded the market in recent years, and there’s typically no way to easily patch these devices. While many businesses have thought security for IoT devices unnecessary because nothing is stored on the devices, this isn’t the case. The Mirai botnet attack illustrated how exposed companies can be as a result of their IoT devices.
Even though these devices continue to be an easy target for cyberattacks, enterprises can take steps to reduce the risk. To start with, default credentials must be changed to something more secure. As employees bring in devices, they should be encouraged to ensure that their passwords are strong and their firmware is always up to date. IoT devices should also be installed on isolated networks (to prevent lateral movement), with restrictions on inbound and outbound network traffic.
Furthermore, access to IoT devices should be restricted as much as possible from external networks, with unnecessary ports blocked from external access. Regular security and firmware updates must also be applied to these devices, in addition to securing the network traffic. Finally, organisations must have visibility of the shadow IoT devices that are already sitting inside the network and ensure that the above safeguards have been implemented.
With all of these new connected devices, and the enormous amounts of associated data traversing corporate networks and opening up new attack vectors for cybercriminals, legacy networks are unlikely to provide adequate security. The threat landscape has changed dramatically and enterprises must not be slow to respond.
The author is Deepen Desai of Zscaler.
Comment on this article below or via Twitter: @IoTNow_OR @jcIoTnow